Google Cloud Storage best practices: how to help ensure data privacy ...
Jan 12, 2021 · Beyond the fundamentals, Cloud Storage offers several security features, such as uniform bucket-level access, service account HMAC keys, IAM conditions, Delegation tokens, and …
Mastering secure AI on Google Cloud, a practical guide for enterprises
Mar 21, 2025 · Sensitive Data Protection can secure AI data on Google Cloud by discovering, classifying, and protecting sensitive information and maintaining data integrity. Cloud Key …
Authenticate for using client libraries - Google Cloud
5 days ago · When you use API keys in your applications, ensure that they are kept secure during both storage and transmission. Publicly exposing your API keys can lead to unexpected charges on your …
Cybersecurity solutions: SecOps, intelligence, AI, and cloud security
Secure your organization with Google Cloud. Get AI-powered SecOps, threat intelligence, and the most trusted cloud security to stay ahead of threats.
Signed URLs | Cloud Storage | Google Cloud Documentation
Feb 17, 2026 · This page provides an overview of signed URLs, which use signatures to give time-limited access to a specific Cloud Storage resource. Anyone in possession of the signed URL can …
Securing Cryptocurrency Organizations | Google Cloud Blog
Jan 21, 2025 · Effective and secure management of secrets within cryptocurrency organizations is critical, even more so than for organizations in other industries. The theft of secrets used to secure …
Cloud Architecture Guidance and Topologies - Google Cloud
Storage Design an optimal storage strategy for your cloud workloads using object, file, block, and archive storage solutions.
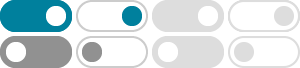
Cloud Storage
Cloud Storage offers secure-by-design features to protect your data and advanced controls and capabilities to keep your data private and secure against leaks or compromises.
Connect using the Cloud SQL Auth Proxy
6 days ago · The Cloud SQL Auth Proxy is a connector that provides secure access to this instance without a need for authorized networks or for configuring SSL. To allow Cloud SQL Auth Proxy client …
Cloud HSM architecture | Security | Google Cloud Documentation
Feb 12, 2026 · You must use the Cloud KMS service endpoint to create and use hardware-protected keys in Cloud HSM to protect your data, including data that you store in other Google Cloud services, …